Overthewire Bandit Challenges Writeup
► Level 0
The goal of this level is for you to log into the game using SSH. The host to which you need to connect is bandit.labs.overthewire.org, on port 2220. The username is bandit0 and the password is bandit0. Once logged in, go to the Level 1 page to find out how to beat Level 1.
Login with username bandit0 and password bandit0, easypeasy!
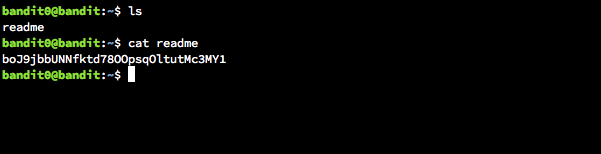
► Level 1
The password for the next level is stored in a file called readme located in the home directory. Use this password to log into bandit1 using SSH. Whenever you find a password for a level, use SSH (on port 2220) to log into that level and continue the game.
► Level 2
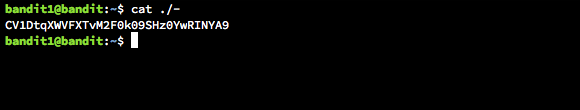
The password for the next level is stored in a file called - located in the home directory.
cat ./-
► Level 3
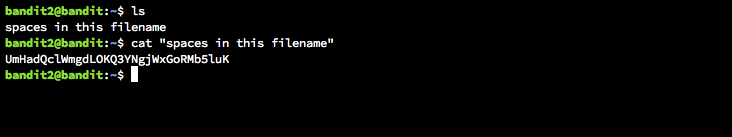
The password for the next level is stored in a file called spaces in this filename located in the home directory
Use quotes to enclose the file with spaces.
cat "spaces in this filename"
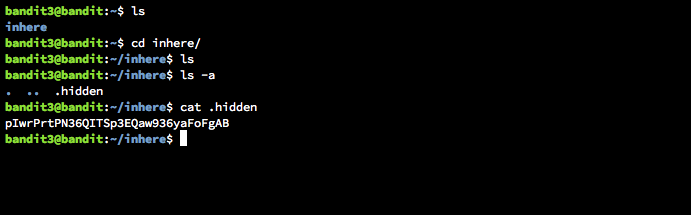
► Level 4
The password for the next level is stored in a hidden file in the inhere directory.
list the hidden file with ls -a and cat it.
► Level 5
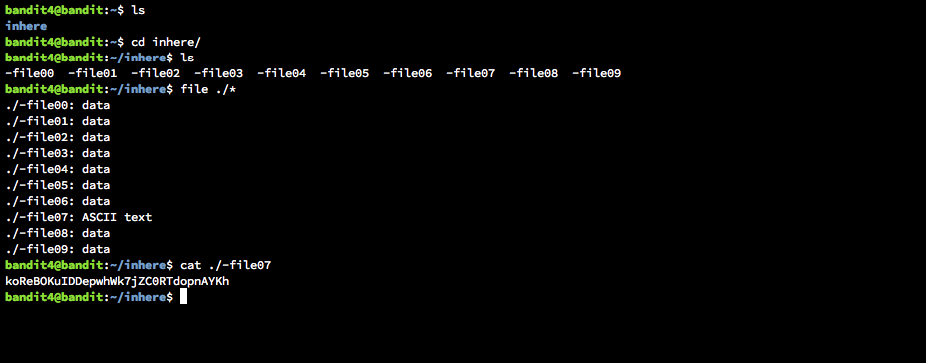
The password for the next level is stored in the only human-readable file in the inhere directory. Tip: if your terminal is messed up, try the “reset” command.
Run file on each and cat the one with ASCII text.
► Level 6
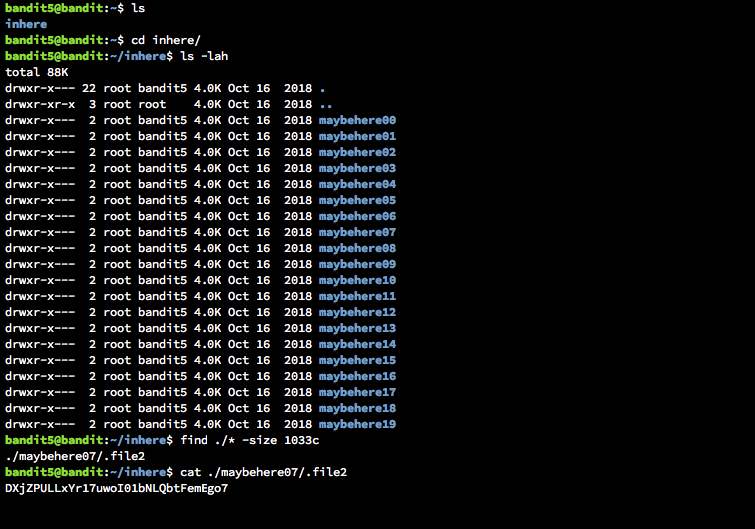
The password for the next level is stored in a file somewhere under the inhere directory and has all of the following properties:
human-readable 1033 bytes in size not executable
Find the file with the size
find ./* -size 1033c
► Level 7
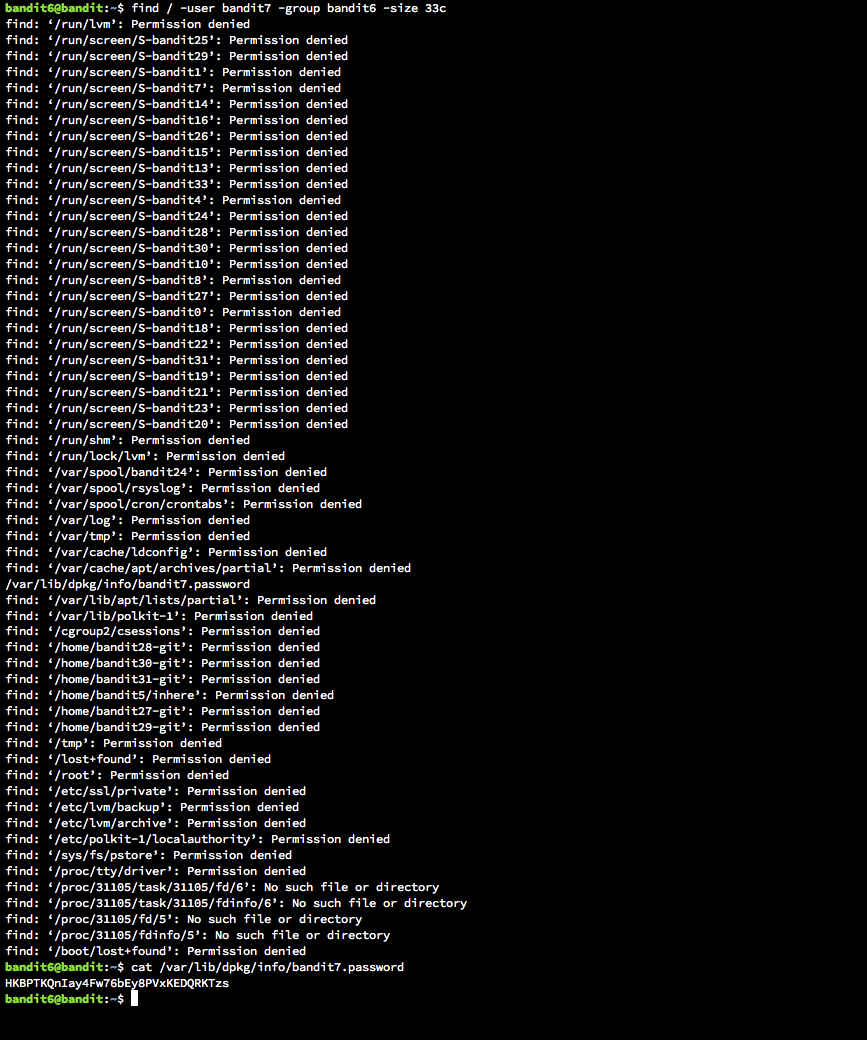
The password for the next level is stored somewhere on the server and has all of the following properties:
owned by user bandit7 owned by group bandit6 33 bytes in size
Find the file in the root directory with group and user flags
find / -user bandit7 -group bandit6 -size 33c
► Level 8
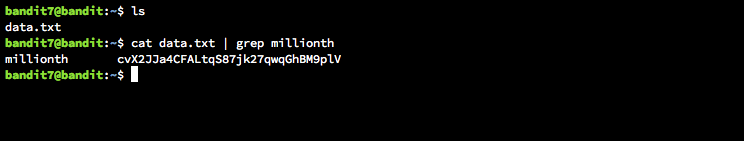
The password for the next level is stored in the file data.txt next to the word millionth
cat data.txt | grep millionth
► Level 9
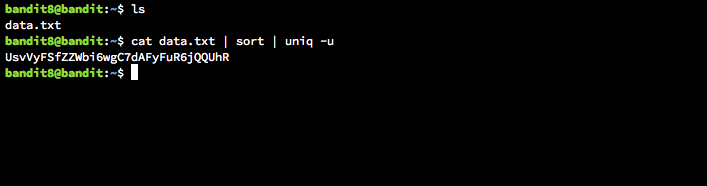
The password for the next level is stored in the file data.txt and is the only line of text that occurs only once
cat data.txt | sort | uniq -u
► Level 10
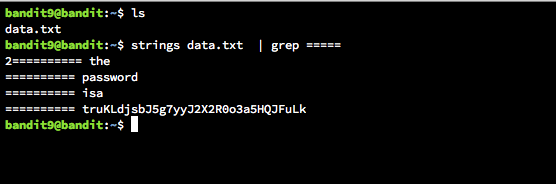
The password for the next level is stored in the file data.txt in one of the few human-readable strings, beginning with several ‘=’ characters.
strings data.txt | grep =====
► Level 11
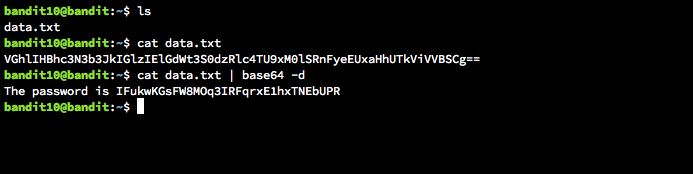
The password for the next level is stored in the file data.txt, which contains base64 encoded data
cat data.txt | base64 -d
► Level 12
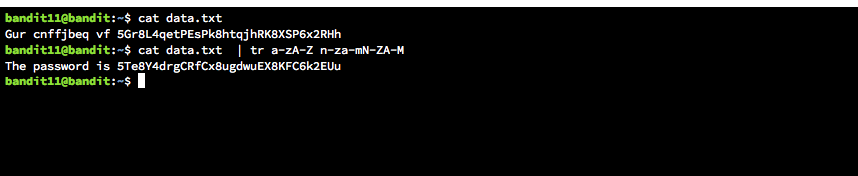
The password for the next level is stored in the file data.txt, where all lowercase (a-z) and uppercase (A-Z) letters have been rotated by 13 positions
cat data.txt | tr a-zA-Z n-za-mN-ZA-M
► Level 13
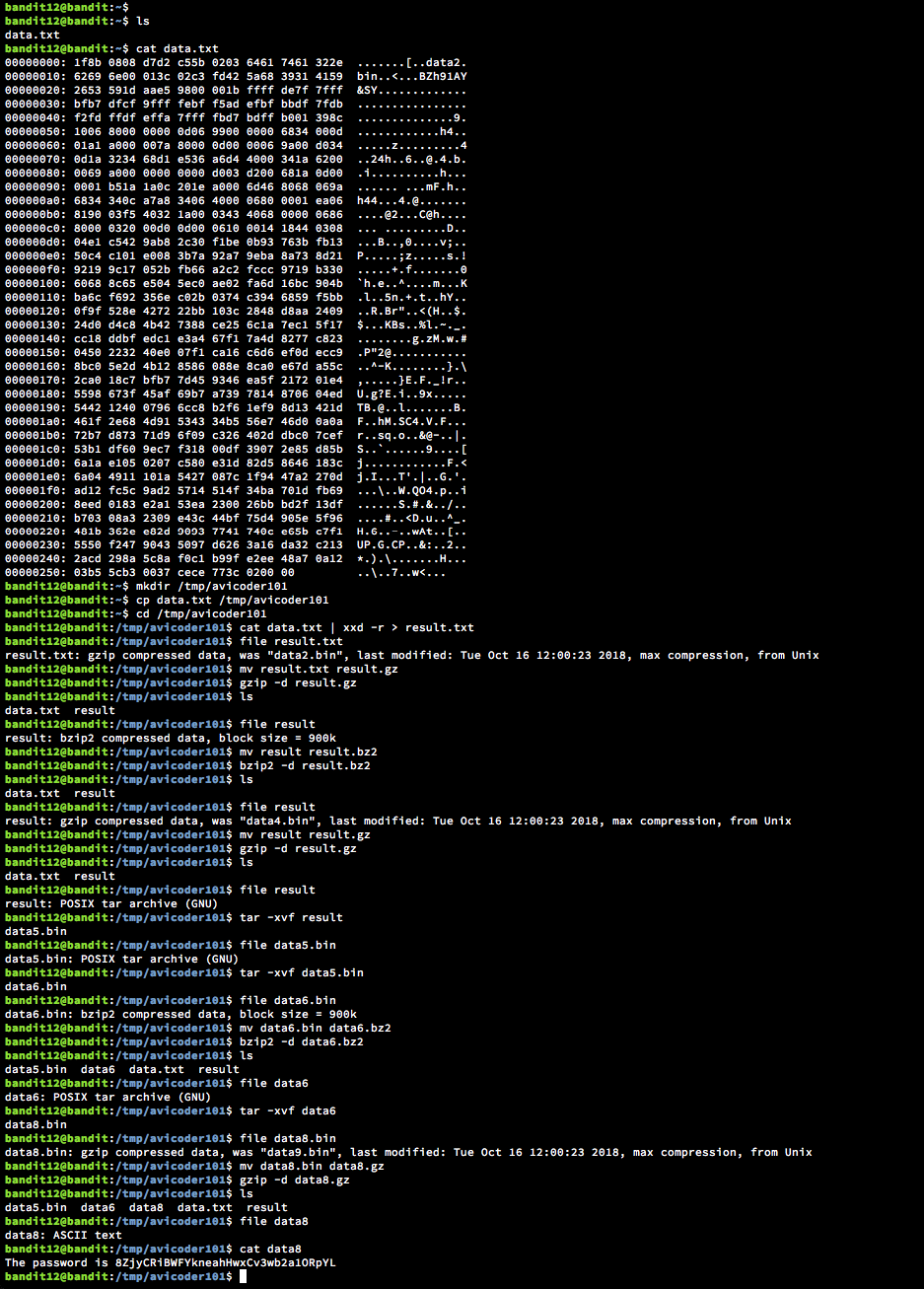
The password for the next level is stored in the file data.txt, which is a hexdump of a file that has been repeatedly compressed. For this level it may be useful to create a directory under /tmp in which you can work using mkdir. For example: mkdir /tmp/myname123. Then copy the datafile using cp, and rename it using mv (read the manpages!)
Lazy to type all the commands - Please check the screenshot.
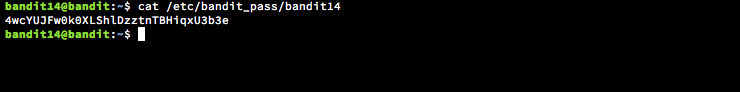
► Level 14
The password for the next level is stored in /etc/bandit_pass/bandit14 and can only be read by user bandit14. For this level, you don’t get the next password, but you get a private SSH key that can be used to log into the next level. Note: localhost is a hostname that refers to the machine you are working on.
ssh -i sshkey.private bandit14@localhost
cat /etc/bandit_pass/bandit14
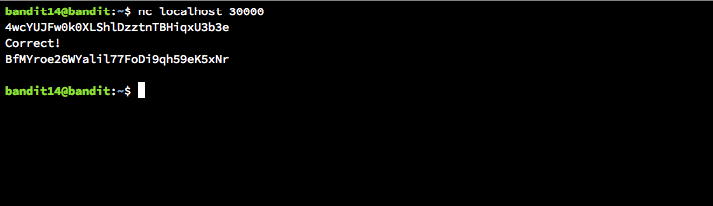
► Level 15
The password for the next level can be retrieved by submitting the password of the current level to port 30000 on localhost.
nc localhost 30000
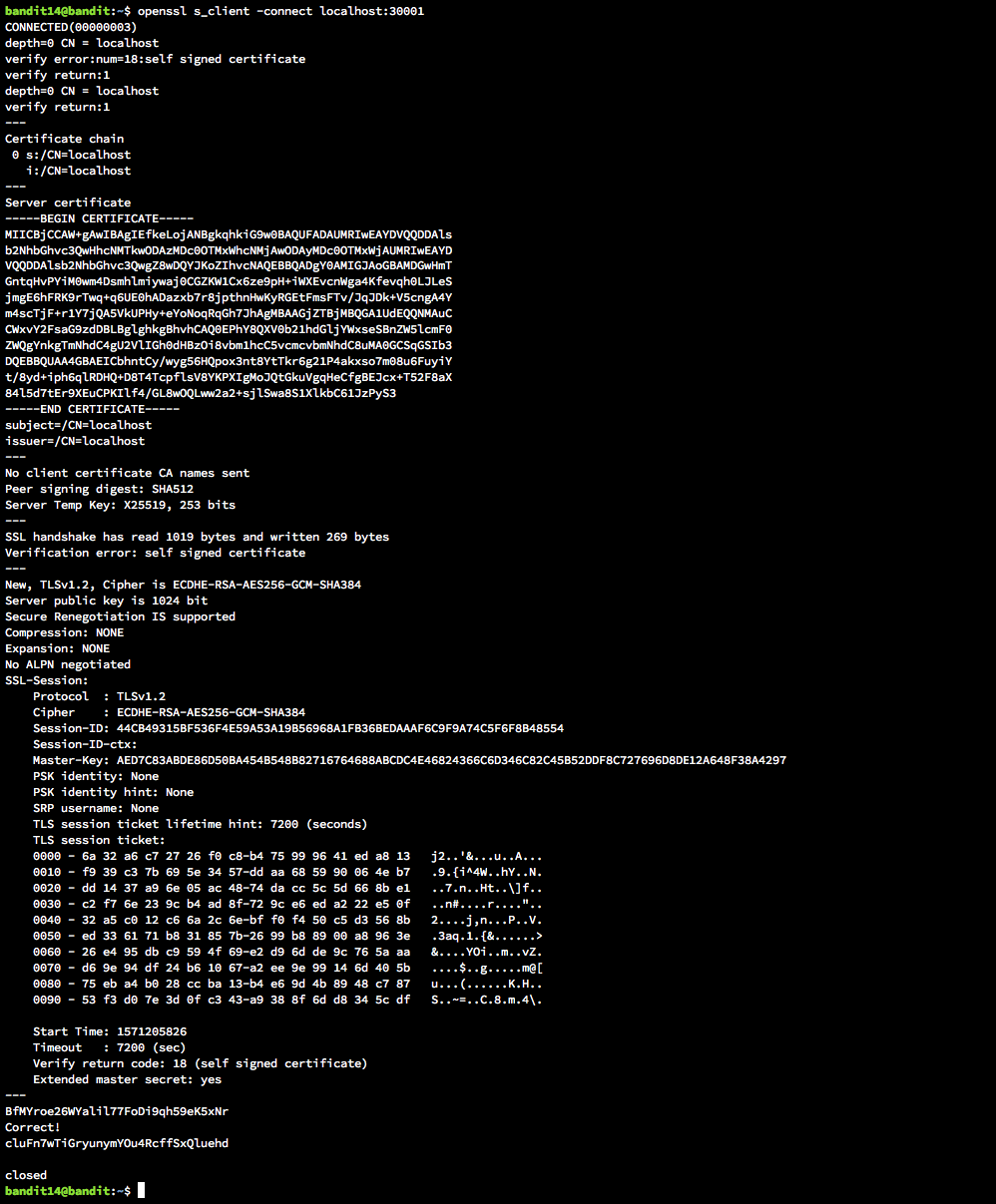
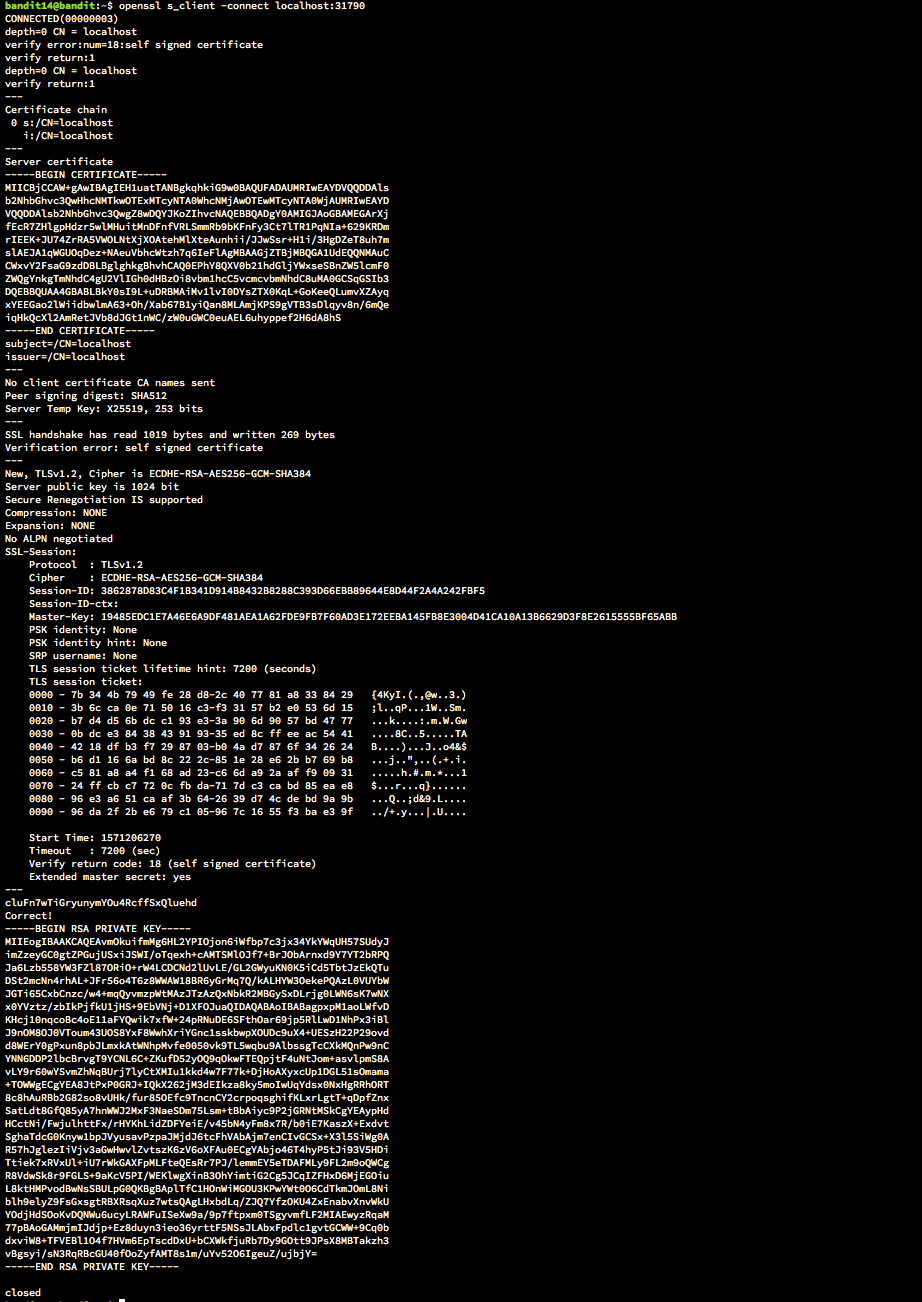
► Level 16
The password for the next level can be retrieved by submitting the password of the current level to port 30001 on localhost using SSL encryption.
Helpful note: Getting “HEARTBEATING” and “Read R BLOCK”? Use -ign_eof and read the “CONNECTED COMMANDS” section in the manpage. Next to ‘R’ and ‘Q’, the ‘B’ command also works in this version of that command…
openssl s_client -connect localhost:30001
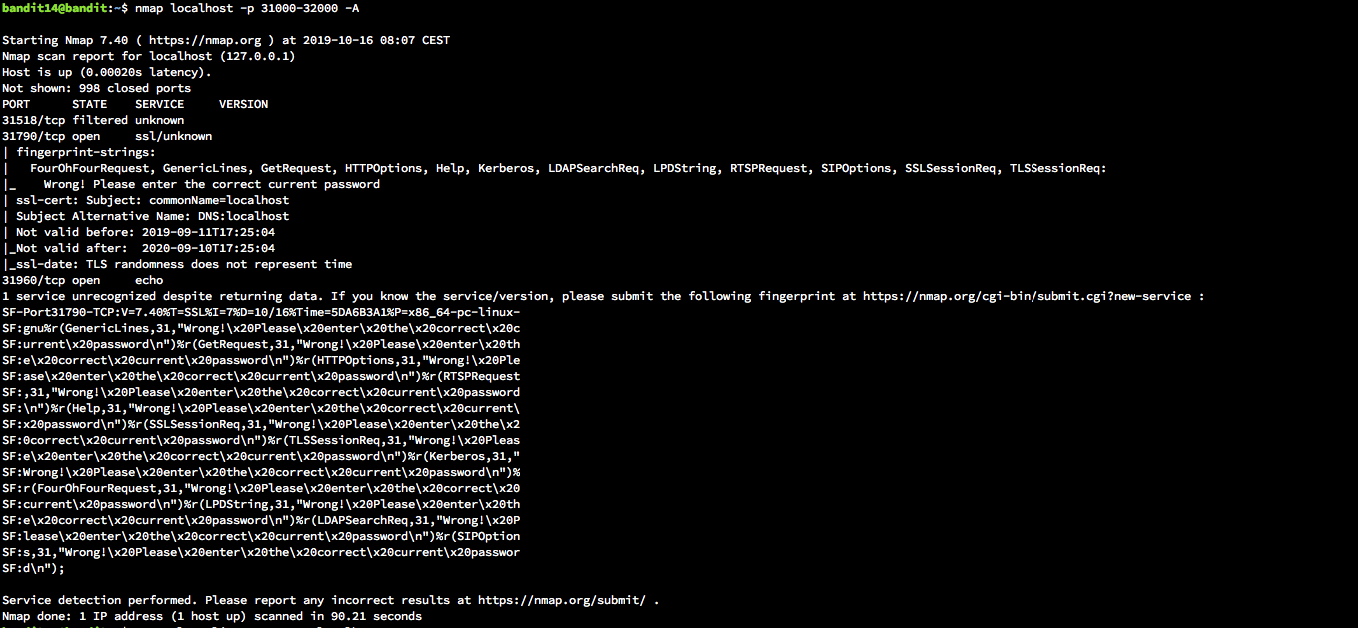
► Level 17
The credentials for the next level can be retrieved by submitting the password of the current level to a port on localhost in the range 31000 to 32000. First find out which of these ports have a server listening on them. Then find out which of those speak SSL and which don’t. There is only 1 server that will give the next credentials, the others will simply send back to you whatever you send to it.
` nmap localhost -p 31000-32000 -A`
openssl s_client -connect localhost:31790
` ssh -i ssh.key bandit17@localhost`
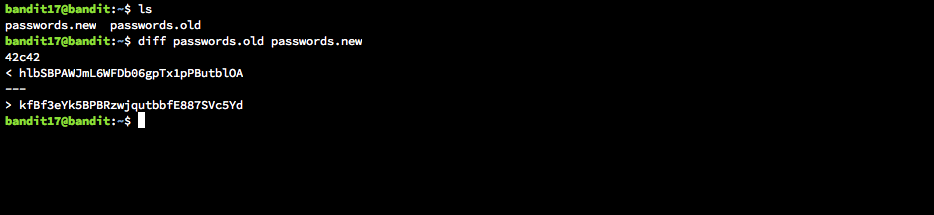
► Level 18
There are 2 files in the homedirectory: passwords.old and passwords.new. The password for the next level is in passwords.new and is the only line that has been changed between passwords.old and passwords.new
NOTE: if you have solved this level and see ‘Byebye!’ when trying to log into bandit18, this is related to the next level, bandit19
diff passwords.old passwords.new
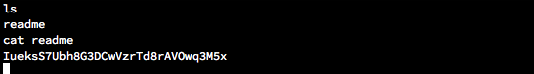
► Level 19
The password for the next level is stored in a file readme in the homedirectory. Unfortunately, someone has modified .bashrc to log you out when you log in with SSH.
` ssh -T bandit18@localhost`
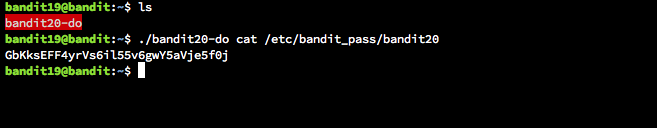
► Level 20
There is a setuid binary in the homedirectory that does the following: it makes a connection to localhost on the port you specify as a commandline argument. It then reads a line of text from the connection and compares it to the password in the previous level (bandit20). If the password is correct, it will transmit the password for the next level (bandit21).
NOTE: Try connecting to your own network daemon to see if it works as you think
./bandit20-do cat /etc/bandit_pass/bandit20
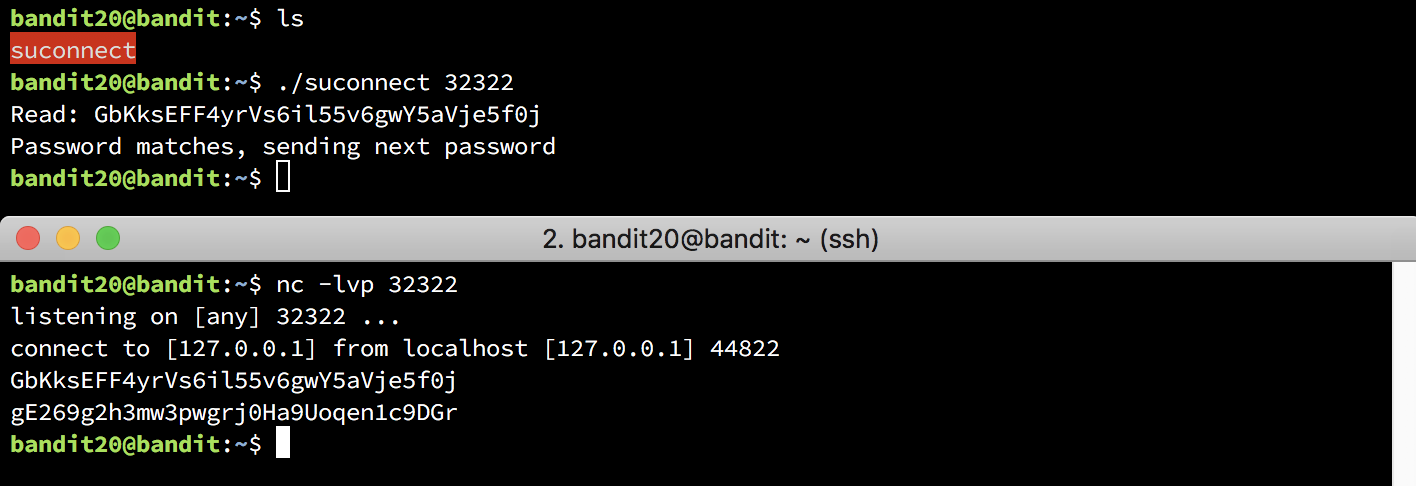
► Level 21
There is a setuid binary in the homedirectory that does the following: it makes a connection to localhost on the port you specify as a commandline argument. It then reads a line of text from the connection and compares it to the password in the previous level (bandit20). If the password is correct, it will transmit the password for the next level (bandit21).
NOTE: Try connecting to your own network daemon to see if it works as you think
./suconnect 32322
nc -lvp 32322
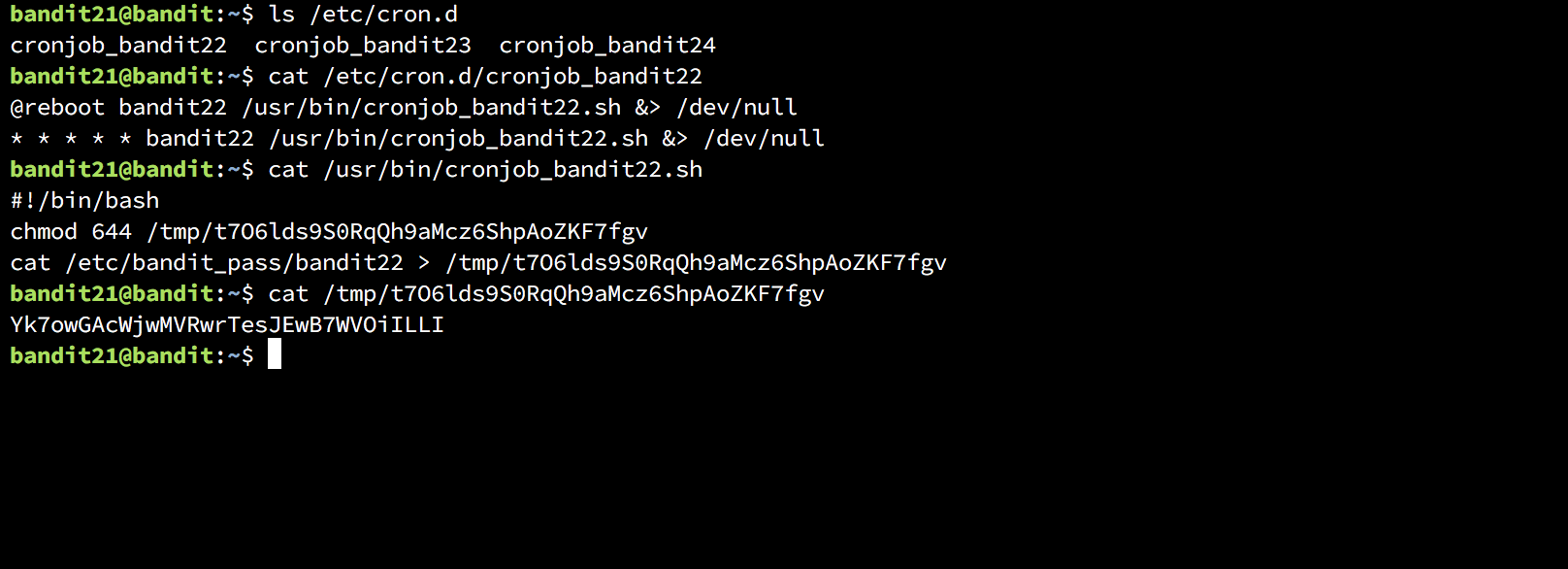
► Level 22
A program is running automatically at regular intervals from cron, the time-based job scheduler. Look in /etc/cron.d/ for the configuration and see what command is being executed.
ls /etc/cron.d cat /etc/cron.d/cronjob_bandit22 cat /usr/bin/cronjob_bandit22.sh cat /tmp/t7O6lds9S0RqQh9aMcz6ShpAoZKF7fgv
► Level 23
A program is running automatically at regular intervals from cron, the time-based job scheduler. Look in /etc/cron.d/ for the configuration and see what command is being executed.
NOTE: Looking at shell scripts written by other people is a very useful skill. The script for this level is intentionally made easy to read. If you are having problems understanding what it does, try executing it to see the debug information it prints.